Thieves are using a built-in setting on every iPhone called the “recovery key” against the owners of stolen iPhones. In theory, the recovery key is there for your protection. It’s a form of two-factor-authentication, known as “2FA” in the industry.
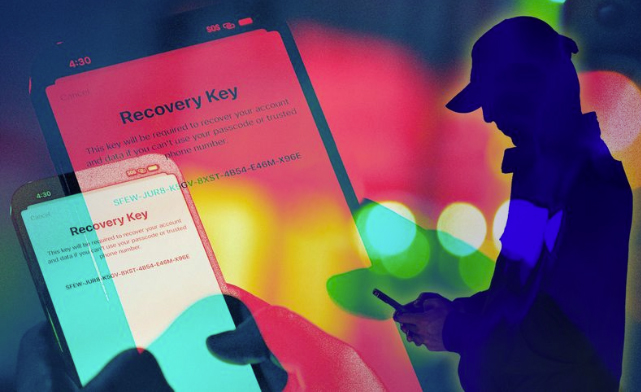
The recovery key is an additional 28-digit code that can be used to access and reset your Apple Account — where all of your contacts, photos, and other personal data is secured. If your phone is lost, stolen, or otherwise compromised, this makes getting everything back much easier.
However, if a thief has your iPhone and passcode, they can enable or reset the recovery key, meaning that they have access to your Apple Account…and you don’t.
As reported in the Wall Street Journal:
“In February, we reported that thieves, often in and around bars at night, watch iPhone owners tap in their passcodes, then steal the targets’ phones. With this short four- or six-digit string, criminals can change the Apple account password and rack up thousands of dollars in charges using Apple Pay and financial apps.
Dozens of victims contacted The Wall Street Journal after the report was published, confirming similar crimes in at least nine U.S. cities, including New York, New Orleans, Chicago and Boston. Those locked out of their Apple accounts by thieves using the recovery key face a bigger challenge: finding a way through Apple’s complex policies and bureaucracy to retrieve their lost photos, contacts, notes, messages and other files.”
Read the full story here.
What can you do?
First of all, be careful when accessing your phone in public. Make sure no one is looking when taping in your digits. Then put it back in your pocket. Don’t leave it on the table while you’re likely to get distracted.
Second, use a complicated passcode, or better yet, use Face ID while in public. That way no one can look over your shoulder while you’re entering your passcode.
The third option is to use the built-in Parental Controls against yourself. This requires an additional Screen Time passcode, but you can set up your Screen Time session to disallow Account Changes. This way, even if a thief can access your phone, they can’t reset your recovery key to block you out of your Apple Account.
Stay safe out there. If you have security concerns regarding any of your devices, Apple or otherwise, give us a call. Our team is here to help.









 March 31st is World Backup Day. Take Action Now!
March 31st is World Backup Day. Take Action Now!

